Have you been following the IRS Don’t Take the Bait series? This 10-part education series was part of the IRS Security Summit effort. Data breaches and scams have been steadily increasing and are getting more and more sophisticated. The purpose of the series is to raise awareness of this and educate tax preparers on security measures and best practices.
IRS Security Summit effort. Data breaches and scams have been steadily increasing and are getting more and more sophisticated. The purpose of the series is to raise awareness of this and educate tax preparers on security measures and best practices.
As tax preparers, it is our responsibility to do our due diligence and protect taxpayer information. We need to be cautious about everything we do and remain hyper-vigilant when it comes to security.
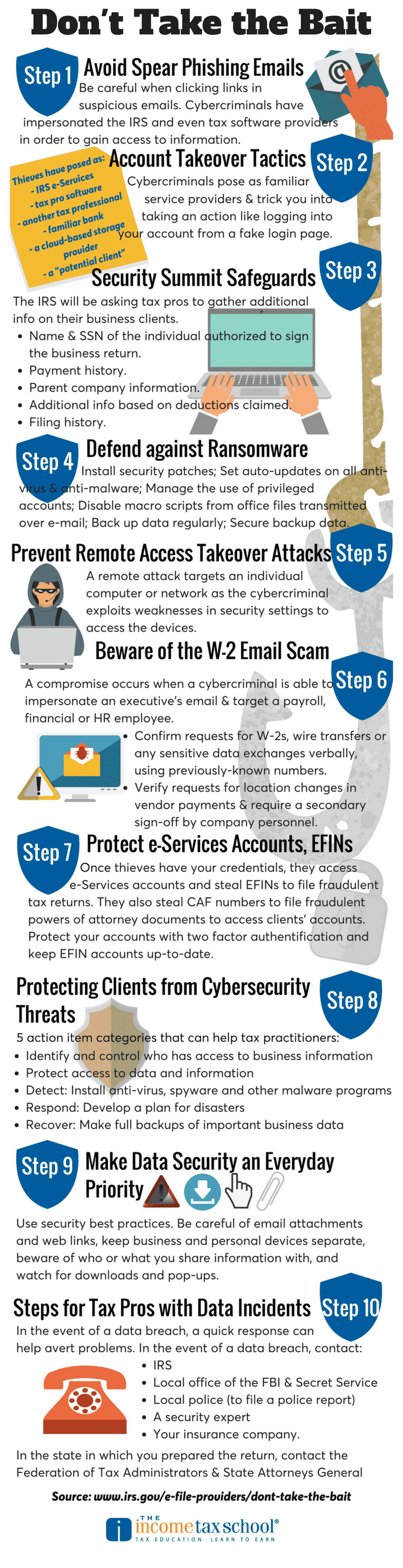
We’ve been following the “Don’t Take the Bait” series since day one. Here’s a recap of all 10 steps with a handy infographic that summarizes them all.
Step 1: Avoid Spear Fishing Emails
We’ve written about phishing scams and how they work before. The IRS warns that these kind of scams are usually tailored to individual practitioners. If you fall prey to one, it usually results in stolen taxpayer data and fraudulent tax returns filed in the names of individual and business clients.
The email is usually disguised as being from a trusted source. It often attempts to get victims to voluntarily disclose sensitive information such as passwords. Or, it may encourage people to open a link or attachment that actually downloads malware onto the computer. The IRS warns tax preparers to be wary of emails they receive – especially when they are asking for sensitive information.
Here are the steps the IRS suggests taking:
- Educate all employees about phishing in general and spear phishing in particular.
- Use strong, unique passwords. Better yet, use a phrase instead of a word. Use different passwords for each account. Use a mix of letters, numbers and special characters.
- Never take an email from a familiar source at face value; example: an email from “IRS e-Services.” If it asks you to open a link or attachment, or includes a threat to close your account, think twice. Visit the e-Services website for confirmation.
- If an email contains a link, hover your cursor over the link to see the web address (URL) destination. If it’s not a URL you recognize or if it’s an abbreviated URL, don’t open it.
- Consider a verbal confirmation by phone if you receive an email from a new client sending you tax information or a client requesting last-minute changes to their refund destination.
- Use security software to help defend against malware, viruses and known phishing sites and update the software automatically.
- Use the security options that come with your tax preparation software.
- Send suspicious tax-related phishing emails to phishing@irs.gov.
Step 2: Be Alert to Account Takeover Tactics
Step 3: Security Summit Safeguards
There are several safeguards the IRS is taking to protect against hackers. For 2018, the IRS will be asking tax pros to gather the following information on their business clients.
- The name and Social Security number of the company individual authorized to sign the business return. Is the person signing the return authorized to do so?
- Payment history – were estimated tax payments made? If yes, when were they made, how were they made, and how much was paid?
- Parent company information – Is there a parent company? If yes who?
- Additional information based on deductions claimed.
- Filing history – Has the business filed Form(s) 940, 941 or other business related tax forms?
Step 4: Defend against Ransomware
Ransomware is a type of malware that infects computers, networks and servers and encrypts (locks) data. Once the malware is on your computer, cybercriminals demand a ransom to release the data. There have only been a handful of tax practitioners who have been victimized by ransomware attacks, but that doesn’t mean there won’t be more. Ransomware attacks are a growing and evolving crime threatening the private and public sectors as well as individuals.
Tips to Prevent Ransomware Attacks
- Make sure employees are aware of ransomware and of their critical roles in protecting the organization’s data.
- For digital devices, ensure that security patches are installed on operating systems, software and firmware. This step may be made easier through a centralized patch management system.
- Ensure that antivirus and anti-malware solutions are set to automatically update and conduct regular scans.
- Manage the use of privileged accounts — no users should be assigned administrative access unless necessary, and only use administrator accounts when needed.
- Configure computer access controls, including file, directory and network share permissions, appropriately. If users require read-only information, do not provide them with write-access to those files or directories.
- Disable macro scripts from office files transmitted over e-mail.
- Implement software restriction policies or other controls to prevent programs from executing from common ransomware locations, such as temporary folders supporting popular Internet browsers, compression/decompression programs.
- Back up data regularly and verify the integrity of those backups.
- Secure backup data. Make sure the backup device isn’t constantly connected to the computers and networks they are backing up. This will ensure the backup data remains unaffected by ransomware attempts.
Step 5: Prevent Remote Access Takeover Attacks
Your entire digital network could be at risk for remote takeover by cybercriminals. Such a takeover could lead to fraudulent tax filings and damage to your clients. A remote attack targets an individual computer or network as the cybercriminal exploits weaknesses in security settings to access the devices. Another line of attack uses malware to download malicious code that gives the criminals access to the network.
The IRS urges tax professionals to take the following steps to help protect themselves from remote takeovers:
- Educate staff members about the dangers of phishing scams, which can be in the form of emails, texts and calls, as well as the threat posed by remote access attacks;
- Use strong security software, set it to update automatically and run a periodic security “deep scan” to search for viruses and malware;
- Identify and assess wireless devices connected to the network, including mobile phones, computers, printers, fax machines, routers, modems and televisions. Replace factory password settings with strong passwords.
- Strengthen passwords for devices and for software access. Make sure passwords are a minimum of eight digits (more is better) with a mix of numbers, letters and special characters;
- Be alert for phishing scams: do not click on links or open attachments from unknown, unsolicited or suspicious senders;
- Review any software that employees use to remotely access the network as well as those used by IT support vendors to remotely troubleshoot technical problems. Remote access software is a potential target for bad actors to gain entry and take control of a machine. Disable remote access software until it is needed.
Step 6: Watch Out for the W-2 Email Scam
The W-2 scam – called a business email compromise or BEC – is one of the most dangerous phishing email schemes trending nationwide. A business email compromise occurs when a cybercriminal is able to “spoof” or impersonate a company or organization executive’s email address and target a payroll, financial or human resources employee with a request.
Tax professionals should be very wary of emails that they receive and should educate clients about these scams. Employers, including tax practitioners, should review their policies for sending sensitive data such as W-2s or making wire transfers based solely on an email request.
Step 7: Protect e-Services Accounts, EFINs
A tax professional’s login credentials are highly sought out by cybercriminals. They use them to access IRS e-Services and obtain the EFIN, which allows a criminal to steal your clients’ information. How do they get your login credentials? They use spear phishing emails. The email usually impersonates IRS e-Services in an attempt to trick practitioners into disclosing their username and password.
The IRS asks that tax practitioners:
- Maintain EFINs: once the EFIN application process is complete and an EFIN has been issued, it is important to keep accounts up-to-date.
- Monitor EFINs: During the filing season, check on the EFIN’s status to ensure that it is not being used by others.
- Protect EFINs: Learn to recognize and avoid phishing scams that claim to be from the IRS or e-Services.
Step 8: How to Start Protecting Clients, Businesses from Cybersecurity Threats
All tax practitioners have a legal obligation to protect taxpayer information in their care. That means securing sensitive data from unauthorized disclosure, improper disposal and outright theft.
Tax pros should review Publication 4557 and NIST’s Small Business Information Security: the Fundamentals.
From Publication 4557:
- Take responsibility or assign someone to be responsible for safeguards
- Assess the risks to taxpayer information in offices.
- Make a list of all the locations where taxpayer information is kept.
- Write a plan of how to safeguard taxpayer information.
- Use only service providers who have policies in place to also maintain an adequate level of information protection.
- Monitor, evaluate and adjust security programs as business or circumstances change
5 action-item categories from NIST’s small business guide:
- Identify: Who has access to business information? Conduct background checks and require individual user computer accounts.
- Protect: Limit access to data and information and protect it by following cybersecurity protocol.
- Detect: Install and update anti-virus, spyware and other malware programs.
- Respond: Develop a plan for disasters and information security incidents.
- Recover: Make full backups of important data/information.
Step 9: Make Data Security an Everyday Priority
Data security within a tax professional’s office is only as strong as the least-informed employee. And, security awareness must extend beyond the office into homes. Create a culture within your tax practice that takes cybersecurity seriously. Embed these best practices into your every day procedures. Here are some best practices that should be followed and taught to employees:
- Be careful of email attachments and web links.
- Use separate personal and business computers, mobile devices and accounts.
- Do not connect personal or untrusted storage devices or hardware into computers, mobile devices or networks.
- Be careful downloading software.
- Watch out when providing personal or business information.
- Watch for harmful pop-ups.
- Use strong passwords.
- Conduct online business more securely.
Step 10: Steps for Tax Pros with Data Incidents; Tips to Help Protect Clients, Taxpayers
The final step is all about reporting an incident when it happens. Criminals work quickly so a quick response once a problem is discovered is crucial and can help avert problems. In the event of a data breach or incident, tax professionals should contact the following agencies.
- IRS (your local IRS Stakeholder Liaison)
- FBI (local office)
- Secret Service (local office)
- Local police to file a report
- The Federation of Tax Administrators (StateAlert@taxadmin.org)
- State Attorneys General for each state in which the tax professional prepares returns
- A security expert to determine the cause and scope of the breach
- Insurance companies to report the breach and check coverage
- The Federal Trade Commission
- Credit / identity theft protection
- Credit bureaus
- Clients – Send an individual letter to all victims to inform them of the breach but work with law enforcement on timing.
Cybercrime is serious and should be treated as such. This is a lot of information to take in but it’s important to know how cybercriminals work so that you can educate employees and clients. Stay vigilant and follow these best practices. Download our infographic below to share with clients and employees.